The DeepSeek Revolution: Why 2026 is the Year of Efficient Intelligence
As we enter 2026, the “DeepSeek Shock” of early 2025 has permanently reshaped the AI industry. What was once seen as a disruptive Chinese challenger
As we enter 2026, the “DeepSeek Shock” of early 2025 has permanently reshaped the AI industry. What was once seen as a disruptive Chinese challenger
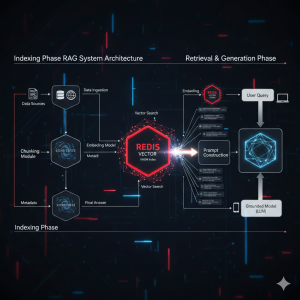
Harness the speed of Redis for RAG systems! Learn what a Redis Vector Store is, when to use it, and how HNSW indexing makes real-time semantic search possible.
Stalkerware is a terrifying form of surveillance software that allows intimate partners or abusers to secretly monitor a victim’s location, messages, calls, and browser history. As this digital abuse escalates, tech companies are fighting back. This article details what stalkerware is, its devastating real-world impact, and how a major update to Google Chrome is directly tackling a key vector—abusive notification prompts and website permissions—to help disrupt the hidden threat and protect users’ privacy.

1) Timeline — the important bits 08:47 UTC (Dec 5, 2025): Cloudflare applied a configuration change intended to protect customers from a disclosed React Server
In the ever-evolving landscape of artificial intelligence, staying ahead of the curve is crucial. Enter DeepSeek V3, the latest iteration of the groundbreaking AI-powered search and

Email remains one of the most common ways for cybercriminals to deceive individuals and organizations. Phishing attacks, spoofing, and other email-based threats can harm your

In a significant shift for developers, JetBrains has announced that its popular IDEs, WebStorm and Rider, are now available for free to non-commercial users. This
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo. The LoveLetter Virus: The Infamous Cyberattack That

Introduction In today’s digital world, the security of data as it travels across the internet is paramount. One of the key technologies ensuring this security
When your Spring Boot application starts consuming an unusual amount of memory, it’s crucial to analyze the memory usage to identify potential issues and optimize

Artificial Intelligence (AI) is revolutionizing industries by providing intelligent solutions to complex problems. OpenAI has been a significant player in this space, but their APIs

Linked lists are a fundamental data structure in computer science, offering a dynamic way to store and manage collections of elements. Unlike arrays, linked

In this blog post, I’ll guide you through the process of integrating with the ChatGPT API to enable automated interactions with OpenAI’s powerful language model.

In this blog post, I guide you through the process of converting an Excel sheet to a JSON file using Node.js. This is particularly useful for tasks such as data migration, data processing, or simply making data more accessible. You’ll learn how to set up your Node.js project, install the necessary packages, and write a script to read an Excel file, convert its contents to JSON, and save the JSON data to a file. By the end of this tutorial, you’ll have a functional script that can be easily adapted to handle different Excel files and sheets as needed.

Introduction In the ever-evolving landscape of cybersecurity, professionals and enthusiasts require tools that can keep up with the rapidly changing threat landscape. Kali Linux, a