
Javascript For Loops
Javascript For Loops in the ECMA Standard Simple For Loop The simplest type of for loop increments a variable as its iteration method. The variable
import java.util.Arrays;
import java.util.List;
import java.util.stream.Collectors;
//------------------------
public class YourClass {
public static void main(String[] args) {
List<String> list = Arrays.asList("a", "b", "c");
String result = list.stream().collect(Collectors.joining(","));
System.out.println(result);
}
}
Output:
a,b,c
import java.util.Arrays;
import java.util.List;
public class MyClass {
public static void main(String[] args) {
List<String> list = Arrays.asList("a","b","c");
String result = String.join(",", list);
System.out.println(result);
}
}
Output:
a,b,c

Javascript For Loops in the ECMA Standard Simple For Loop The simplest type of for loop increments a variable as its iteration method. The variable

Retriving a List of attribute (field) values from a Object List (Array List) List users=new ArrayList<>(); List userIds=users .stream() .map(u->u.getId()) .collect(Collectors.toList()); Filter Objects by Attribute

let message = ‘helloWorld’ let convertedMessage=message.replace(/[A-Z]/g, letter => `_${letter.toLowerCase()}`); console.log(convertedMessage); output -> hello_world How to Convert Camel Case to Snake Case JavaScript
As we enter 2026, the “DeepSeek Shock” of early 2025 has permanently reshaped the AI industry. What was once seen as a disruptive Chinese challenger
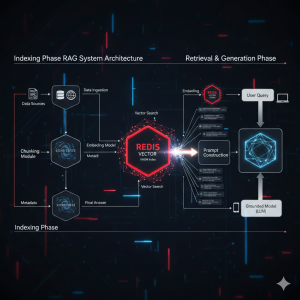
Harness the speed of Redis for RAG systems! Learn what a Redis Vector Store is, when to use it, and how HNSW indexing makes real-time semantic search possible.
Stalkerware is a terrifying form of surveillance software that allows intimate partners or abusers to secretly monitor a victim’s location, messages, calls, and browser history. As this digital abuse escalates, tech companies are fighting back. This article details what stalkerware is, its devastating real-world impact, and how a major update to Google Chrome is directly tackling a key vector—abusive notification prompts and website permissions—to help disrupt the hidden threat and protect users’ privacy.

1) Timeline — the important bits 08:47 UTC (Dec 5, 2025): Cloudflare applied a configuration change intended to protect customers from a disclosed React Server