Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
The LoveLetter Virus: The Infamous Cyberattack That Shook the World
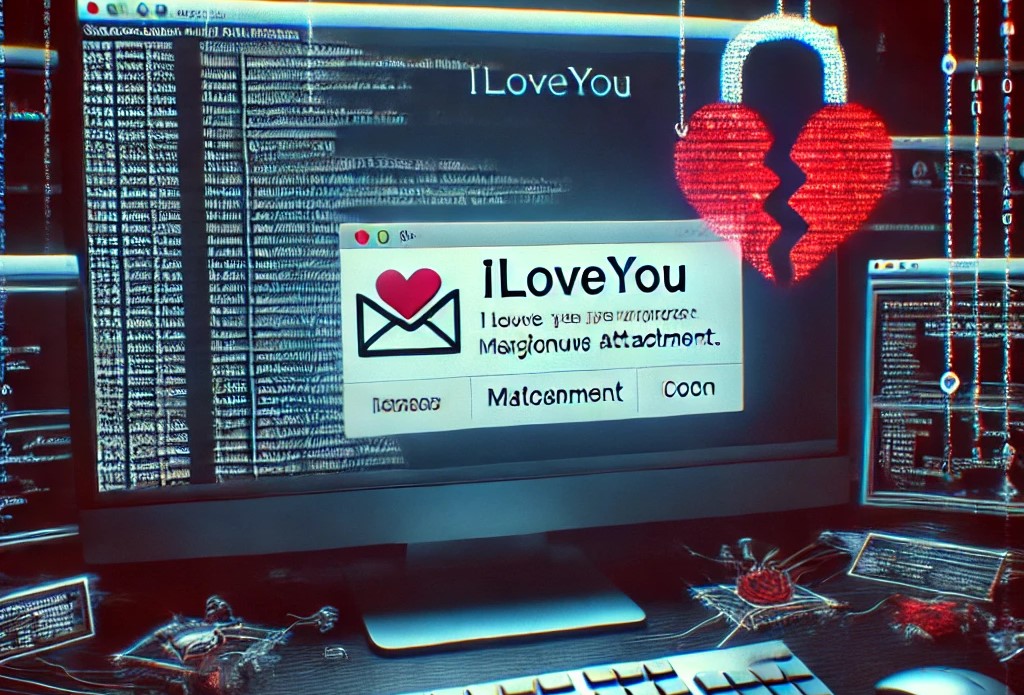
In May 2000, the world witnessed one of the most infamous and destructive cyberattacks in history—the LoveLetter virus. This fast-spreading email worm impacted millions of computers worldwide within just a few hours, leaving businesses and individuals scrambling to contain the damage. Let’s dive into the story of the LoveLetter attack, exploring how it worked, its impact, and the lessons it offers in the modern cybersecurity landscape.
The Birth of the LoveLetter Virus
The LoveLetter virus, also known as ILOVEYOU or the Love Bug, was created by two Filipino computer programmers, Onel de Guzman and Reomel Ramones. The virus was written in VBScript and spread via email with the subject line “ILOVEYOU”. The email contained a simple attachment named LOVE-LETTER-FOR-YOU.TXT.vbs.
Once the unsuspecting recipient opened the file, the virus unleashed itself, replicating and spreading further by sending copies of the same email to every contact in the victim’s address book. What made the virus so effective was its social engineering component: the promise of a love letter, an enticing lure for many users.
How the LoveLetter Virus Worked
The LoveLetter virus operated by exploiting several vulnerabilities in Microsoft Outlook, as well as the tendency for Windows to hide file extensions. Here’s how it worked:
- Email Transmission: The virus disguised itself as a text file (
.TXT.vbs), exploiting the fact that most users were unaware of the hidden.vbsextension, believing it to be a harmless text document. - Self-replication: Once activated, the virus sent itself to all contacts in the user’s email address book, resulting in rapid dissemination.
- File Corruption: It overwrote key files on the infected system, including music, images, and other documents, by appending the
.vbsextension to the file name. - Registry Modification: The virus also made changes to the Windows registry, enabling it to execute every time the system rebooted, making it harder to remove.
The Scale of the Damage
The speed and scale of the LoveLetter virus’s spread were unprecedented at the time. Within hours, it infected more than 45 million systems globally, affecting organizations ranging from banks to government agencies. The total damage was estimated at over $10 billion, both from the destruction of files and the disruption of business operations.
Major companies, including Ford, AT&T, and the Pentagon, were forced to shut down their email systems to prevent further infection. It became clear that cybersecurity had become a global issue.
LoveLetter’s Global Impact
The LoveLetter virus not only caused financial damage but also spurred a global conversation on cybersecurity vulnerabilities. It led to the arrest of Onel de Guzman in the Philippines, but due to the lack of robust cybercrime laws at the time, the perpetrators were not prosecuted. This case highlighted the urgent need for international legislation on cybercrime.
Lessons from the LoveLetter Attack
Even though the LoveLetter virus was written over two decades ago, it offers valuable lessons that remain relevant today:
-
Social Engineering: The success of the LoveLetter virus hinged on tricking people into clicking on something that appeared harmless. Today, phishing emails and other forms of social engineering continue to be a primary vector for cyberattacks. Educating users on how to recognize suspicious messages is critical to preventing future attacks.
-
Patching and Security Updates: The LoveLetter virus exploited vulnerabilities in Microsoft Outlook. Keeping software up to date with the latest security patches is one of the most effective ways to defend against such exploits.
-
Backup Strategies: As the virus corrupted important files, many organizations and individuals lost valuable data. Having a solid data backup strategy is essential to minimize the impact of malware that destroys or locks files, such as ransomware.
-
Email Security: Email remains one of the most common ways for malware to spread. Implementing strong email filtering, disabling auto-execution of attachments, and scanning incoming attachments for malware can prevent similar incidents.
Modern Malware Inspired by LoveLetter
While technology has advanced since 2000, the LoveLetter virus laid the foundation for many of today’s threats. Modern attacks like ransomware, business email compromise (BEC), and phishing scams often employ social engineering tactics similar to the ones used by LoveLetter.
The attack also highlighted the fact that, even as technical defenses improve, human behavior remains one of the weakest links in cybersecurity. Malware authors continually refine their methods, but many rely on the same basic principles of deception that made LoveLetter so effective.
Conclusion
The LoveLetter virus remains a cautionary tale in the annals of cybersecurity history. Its devastating effects, rapid spread, and reliance on human behavior continue to serve as a reminder of the importance of cybersecurity awareness. Although malware has evolved significantly since the LoveLetter virus first hit, the lessons learned from this attack remain as relevant today as they were two decades ago. As we move into an increasingly connected digital world, understanding and defending against the tactics employed by past attacks is essential to staying safe in the future.
Common attacks and their effectiveness
Previously, you learned about past and present attacks that helped shape the cybersecurity industry. These included the LoveLetter attack, also called the ILOVEYOU virus, and the Morris worm. One outcome was the establishment of response teams, which are now commonly referred to as computer security incident response teams (CSIRTs). In this reading, you will learn more about common methods of attack. Becoming familiar with different attack methods, and the evolving tactics and techniques threat actors use, will help you better protect organizations and people.
Phishing
Phishing is the use of digital communications to trick people into revealing sensitive data or deploying malicious software.
Some of the most common types of phishing attacks today include:
Business Email Compromise (BEC): A threat actor sends an email message that seems to be from a known source to make a seemingly legitimate request for information, in order to obtain a financial advantage.
Spear phishing: A malicious email attack that targets a specific user or group of users. The email seems to originate from a trusted source.
Whaling: A form of spear phishing. Threat actors target company executives to gain access to sensitive data.
Vishing: The exploitation of electronic voice communication to obtain sensitive information or to impersonate a known source.
Smishing: The use of text messages to trick users, in order to obtain sensitive information or to impersonate a known source.
Malware
Malware is software designed to harm devices or networks. There are many types of malware. The primary purpose of malware is to obtain money, or in some cases, an intelligence advantage that can be used against a person, an organization, or a territory.
Some of the most common types of malware attacks today include:
Viruses: Malicious code written to interfere with computer operations and cause damage to data and software. A virus needs to be initiated by a user (i.e., a threat actor), who transmits the virus via a malicious attachment or file download. When someone opens the malicious attachment or download, the virus hides itself in other files in the now infected system. When the infected files are opened, it allows the virus to insert its own code to damage and/or destroy data in the system.
Worms: Malware that can duplicate and spread itself across systems on its own. In contrast to a virus, a worm does not need to be downloaded by a user. Instead, it self-replicates and spreads from an already infected computer to other devices on the same network.
Ransomware: A malicious attack where threat actors encrypt an organization’s data and demand payment to restore access.
Spyware: Malware that’s used to gather and sell information without consent. Spyware can be used to access devices. This allows threat actors to collect personal data, such as private emails, texts, voice and image recordings, and locations.
Social Engineering
Social engineering is a manipulation technique that exploits human error to gain private information, access, or valuables. Human error is usually a result of trusting someone without question. It’s the mission of a threat actor, acting as a social engineer, to create an environment of false trust and lies to exploit as many people as possible.
Some of the most common types of social engineering attacks today include:
Social media phishing: A threat actor collects detailed information about their target from social media sites. Then, they initiate an attack.
Watering hole attack: A threat actor attacks a website frequently visited by a specific group of users.
USB baiting: A threat actor strategically leaves a malware USB stick for an employee to find and install, to unknowingly infect a network.
Physical social engineering: A threat actor impersonates an employee, customer, or vendor to obtain unauthorized access to a physical location.
Social engineering principles
Social engineering is incredibly effective. This is because people are generally trusting and conditioned to respect authority. The number of social engineering attacks is increasing with every new social media application that allows public access to people’s data. Although sharing personal data—such as your location or photos—can be convenient, it’s also a risk.
Reasons why social engineering attacks are effective include:
Authority: Threat actors impersonate individuals with power. This is because people, in general, have been conditioned to respect and follow authority figures.
Intimidation: Threat actors use bullying tactics. This includes persuading and intimidating victims into doing what they’re told.
Consensus/Social proof: Because people sometimes do things that they believe many others are doing, threat actors use others’ trust to pretend they are legitimate. For example, a threat actor might try to gain access to private data by telling an employee that other people at the company have given them access to that data in the past.
Scarcity: A tactic used to imply that goods or services are in limited supply.
Familiarity: Threat actors establish a fake emotional connection with users that can be exploited.
Trust: Threat actors establish an emotional relationship with users that can be exploited over time. They use this relationship to develop trust and gain personal information.
Urgency: A threat actor persuades others to respond quickly and without questioning.